- | Home |
- Company |
- Contact |
- News |
- S/ware Eng |
- Standards |
- Academic Support |
- Documents |

- | Requirements |
- Compilers |
- Validation |
- RTOS |
- Analysis |
- Hardware |
- Software |
- Resources |
- Products |
Segger emSecure-ECDSA

emSecure-ECDSA, offers digital signatures based on the modern elliptic curve digital signature algorithms.
Using elliptic curves requires smaller key sizes for the same level of security. The keys use less memory when stored in an application, the algorithms run faster with smaller numbers, resulting in higher speeds.
With a default key data can be signed in less than 160 ms.
-
Modern algorithm
Fast signature generation
Low RAM usage
Smaller keys for same level of security
Using emSecure-ECDSA
All emSecure products are created to be simple but powerful, and easy to integrate. It can be used in new products and even extend existing ones as emSecure is a software solution and no additional hardware is required. The code is completely written in ANSI C and can be used platform- and controller-independent.
The required key pairs can be generated with the included tool. The generated keys can be exported into different formats to be stored on the application code or loaded from a key file. This allows portability and exchangeability between different platforms.
Signing data, for instance firmware images, can be done immediately with the included tool. It is also possible to integrate the signing process directly into a production application running on any PC or even on a microcontroller.
Once a signature is generated, the signed data can be verified by its signature in an embedded application or on an external application communicating with the device. Verifying data typically takes less than 160 ms on a Cortex-M4, running at 200 MHz, which is not significantly more time for a bootloader to start a firmware
Performance
emSecure-ECDSA aims for portability and is designed to fit speed and size requirements for different targets.
The process of verifying data is technically split up into two steps:
Compute the hash of the data.
Compare the hash value against the one stored in the signature
Step 1, the computation of the hash, depends on the size of the data, whereas step 2 is dependent on the key length and takes the same time to verify any data.
Step |
Performance |
|---|---|
SHA-256 |
5.08 MB/sec |
ECDSA P-256 |
156.18 ms |
ECDSA P-256 |
151.67 ms |
Verifying data
The following table shows some total values to verify different amounts of data.
Data size |
Key curve |
Signature |
Hash |
Total time |
|---|---|---|---|---|
1 kByte |
P-256 |
156.18 ms |
0.20 ms |
156.38 ms |
100 kByte |
P-256 |
156.18 ms |
20.16 ms |
176.34 ms |
Signing data
The following table shows some total values to sign different amounts of data.
Data size |
Key curve |
Signature |
Hash |
Total time |
|---|---|---|---|---|
1 kByte |
P-256 |
151.67 ms |
0.20 ms |
151.82 ms |
100 kByte |
P-256 |
151.67 ms |
20.16 ms |
171.75 ms |
The performance values are for a Cortex-M4 microcontroller, running at 200 MHz.
Memory Footprint
|
ROM |
Static RAM |
Stack |
|---|---|---|---|
P-256 key |
|||
Verification only: |
10.2 KByte |
0 KByte |
2.4 KByte |
Verification & Generation: |
12.2 KByte |
6.2 KByte |
The memory values are for a Cortex-M4 microcontroller.
Included Applications
emSecure includes all basic applications needed for securing a product. The applications' source-code is included and provides an easy to use starting point for modifications and integration into other applications.
Application name |
Target platform |
Description |
|---|---|---|
emKeyGen ECDSA |
Windows |
Generates a key pair with a given curve. |
emSign ECDSA |
Windows |
Digitally signs a file with your private key. |
emVerify ECDSA |
Windows |
Verifies the signature of a digital asset with its public key. |
emPrintKey |
Windows |
Exports keys and signatures into C source format, to be included into any application. |
Utilities
The utilities are PC applications, ready-to-use for the setup step to secure your product.
Key generation
emKeyGen ECDSA generates a public and a private key. The generation parameters can be set with command line options. The keys are saved in a common key file format and can be published and exchanged.
Usage: emKeyGenECDSA.exe [<Options>
Exporting keys
emPrintKey exports key and signature files into a compileable format. The output can be linked into your application, so there is no need to load them from a file at runtime. This is especially useful for embedded applications.
Signing data
emSign ECDSA digitally signs the file content, usually the data to be secured, with a given (private) key file and creates a signature file.
Verifying data
emVerify ECDSA decrypts a signature file and verifies if the corresponding data file matches the signature.
Technical Background
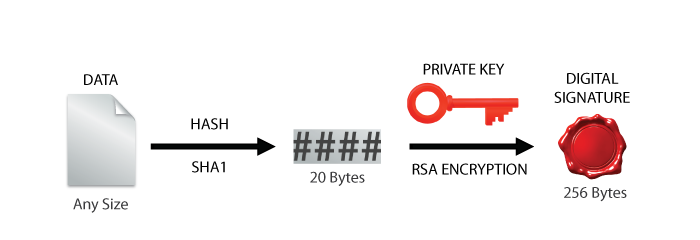
The emSecure signing operation starts by using a secure hash algorithm (SHA1) to generate a hash from the original data. Using the 2kBit RSA private key along with the hash, a digital signature is generated using RSA encryption.
emSecure Signing Technical Details:
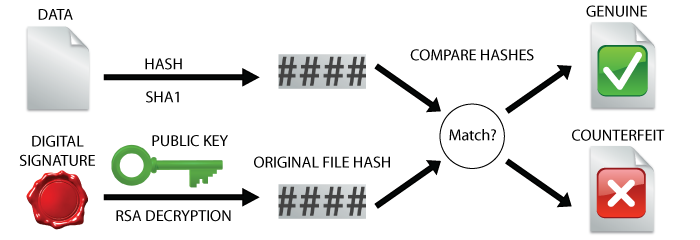
The emSecure-ECDSA verification process starts with the data one wishes to verify and the digital signature which was created from the original file. A hash value is generated for the unverified data. The ECDSA public key is used to extract the original hash from the signature and then compare it with the generated hash to verify whether the data file is genuine or not.
emSecure Verification Technical Details: